Multi-Layer PHP Source Code Protection Model Using Encoding with Integrity Hashing and Anti-Reverse Engineering
##plugins.themes.bootstrap3.article.main##
Abstract
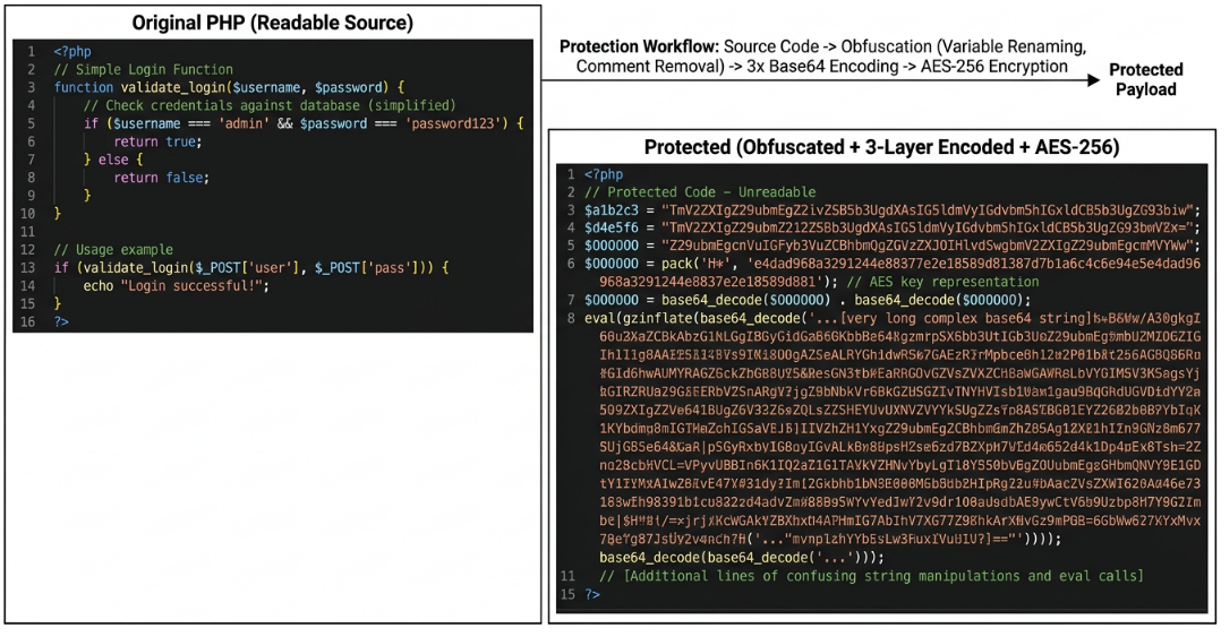
Unprotected PHP source code is vulnerable to reverse engineering, piracy, and illegal modifications. This research aims to design and develop a multi-layer PHP source code protection model that combines obfuscation techniques, multi-layer encoding, AES-256 encryption, and hashing mechanisms with anti-tamper capabilities to maintain code confidentiality and integrity. The system is also equipped with auto-restore features and panic notification via Telegram Bot that automatically restores original files and sends security warnings when illegal changes are detected. The methodology used is Research and Development (R&D), with stages including literature review, system design, prototype development, security experiments, and performance benchmarking. The expected results show that the multi-layer model can hinder reverse engineering, accurately detect file changes, and provide rapid responses via auto-restore and Telegram notifications, significantly improving PHP source code security compared to conventional encoders. The security experiments demonstrated superior protection against deobfuscation attacks, with benchmark results showing acceptable performance overhead (an average execution-time increase of 15-20ms, a CPU load increase of 8-12%, and a memory usage increase of 5-8 MB) compared to commercial encoders.
##plugins.themes.bootstrap3.article.details##

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
Authors who publish articles in CoreID Journal agree to the following terms:
- Authors retain copyright of the article and grant the journal right of first publication with the work simultaneously licensed under a CC-BY-SA or The Creative Commons Attribution–ShareAlike License.
- Authors are able to enter into separate, additional contractual arrangements for the non-exclusive distribution of the journal's published version of the work (e.g., post it to an institutional repository or publish it in a book), with an acknowledgment of its initial publication in this journal.
- Authors are permitted and encouraged to post their work online (e.g., in institutional repositories or on their website) prior to and during the submission process, as it can lead to productive exchanges, as well as earlier and greater citation of published work (See The Effect of Open Access).
References
M. Sigala, A. Beer, L. Hodgson, and A. O’Connor, Big Data for Measuring the Impact of Tourism Economic Development Programmes: A Process and Quality Criteria Framework for Using Big Data. 2019.
G. Nguyen et al., “Machine Learning and Deep Learning frameworks and libraries for large-scale data mining: a survey,” Artif. Intell. Rev., vol. 52, no. 1, pp. 77–124, 2019, doi: 10.1007/s10462-018-09679-z.
C. Collberg and J. Nagra, Surreptitious Software: Obfuscation, Watermarking, and Tamperproofing for Software Protection. Addison-Wesley Professional, 2009.
“PHP obfuscation vs encryption: Which works best?,” SourceGuardian Blog. [Online]. Available: https://www.sourceguardian.com/blog-php-obfuscation-vs-encryption-which-works-best--post-242-1.html
“ionCube PHP encoder - Secure code with powerful encryption,” ionCube. [Online]. Available: https://www.ioncube.com
A. Rahmatulloh and R. Munir, “Pencegahan Ancaman Reverse Engineering Source Code PHP dengan Teknik Obfuscation Code pada Extension PHP,” Tesis Magister, Institut Teknologi Bandung, Bandung, 2016.
O. Setiawan, R. Fiati, and T. Listyorini, “Algoritma Enkripsi RC4 Sebagai Metode Obfuscation Source Code PHP,” in Prosiding SNATIF ke-1 Tahun 2014, Kudus, Indonesia: Muria Kudus University, 2014.
K. Kim, J. Shin, J. Park, and J. Kim, “Performance Evaluations of AI‐Based Obfuscated and Encrypted Malicious Script Detection with Feature Optimization,” ETRI J., vol. 47, no. 4, pp. 753–770, Aug. 2025, doi: 10.4218/etrij.2024-0255.
S. R. Tambunan and N. Rokhman, “C Source code Obfuscation using Hash Function and Encryption Algorithm,” IJCCS Indones. J. Comput. Cybern. Syst., vol. 17, no. 3, p. 227, Jul. 2023, doi: 10.22146/ijccs.86118.
S. Dheyaa Mohammed, A. Monem S. Rahma, and T. Mohammed Hasan, “Maintaining the Integrity of Encrypted Data by Using the Improving Hash Function Based on GF 28,” TEM J., pp. 1277–1284, Aug. 2020, doi: 10.18421/TEM93-57.
A. Chincholkar, A. Londhe, M. Joshi, P. Gole, and S. Mirgale, “Ensuring Confidentiality and Integrity in Cloud Storage Using AES Encryption and SHA-256 Hashing,” Int. J. Eng. Res., vol. 14, no. 10, 2025.
S. Zhao et al., “DEPHP: A Source Code Recovery Method for PHP Bytecode with Improved Structural Analysis,” in 2025 28th International Symposium on Research in Attacks, Intrusions and Defenses (RAID), Gold Coast, Australia: IEEE, Oct. 2025, pp. 77–91. doi: 10.1109/RAID67961.2025.00032.
“How Dynamic Licensing Secures PHP Code Distribution,” SourceGuardian Blog. [Online]. Available: https://www.sourceguardian.com/blog-how-dynamic-licensing-secures-php-code-distribution-post-277-1.html
A. Rahmatulloh and R. Munir, “Pencegahan Ancaman Reverse Engineering Source Code PHP dengan Teknik Obfuscation Code pada Extension PHP,” in Konferensi Nasional Informatika, Bandung, 2015.
A. L. Aprianto and I. Winarno, “Rancang Bangun PHP 5 Encoder,” in Seminar Nasional Teknologi Industri dan Informatika, 2011.
M. L. Assidiq, F. Mahardika, and D. Santika, “Implementasi Algoritma Kriptografi AES dan SHA-3 dalam Mengamankan Data Sensitif Pengguna pada Website Transaksi,” Simpatik J. Sist. Inf. Dan Inform., vol. 4, no. 1, pp. 44–52, Jun. 2024, doi: 10.31294/simpatik.v4i1.3386.
A. Chincholkar, A. Londhe, M. Joshi, P. Gole, and S. Mirgale, “Ensuring Confidentiality and Integrity in Cloud Storage using AES Encryption and SHA-256 Hashing,” Int. J. Eng. Res., vol. 14, no. 10, 2025.
National Institute of Standards and Technology (US), “Secure Hash Standard,” National Institute of Standards and Technology (U.S.), Washington, D.C., NIST FIPS 180-4, 2015. doi: 10.6028/NIST.FIPS.180-4.
N. Ristić and A. Jevremović, “One Solution for Protecting PHP Source Code,” in Proceedings of the 1st International Scientific Conference - Sinteza 2014, Belgrade, Serbia: Singidunum University, 2014, pp. 616–619. doi: 10.15308/sinteza-2014-616-619.
Newsoftwares.net, “Verify Encryption & Integrity : Hashes, Self Checksums, Test Restores,” Verify Encryption & Integrity : Hashes, Self Checksums, Test Restores. Accessed: Apr. 06, 2026. [Online]. Available: https://www.newsoftwares.net/blog/verify-encryption-integrity-hashes-self-checksums-test-restores/
“Telegram bot API documentation,” Telegram. [Online]. Available: https://core.telegram.org/bots/api
Sugiyono, Metode penelitian kuantitatif, kualitatif, dan R&D. Bandung: Alfabeta, 2022.
M. D. Borg, W. R., & Gall, Educational research: An introduction. Boston, MA: Allyn & Bacon, 2003.
J. Lengstorf, PHP for Absolute Beginners. Appres, 2009.
D. Susanto, Risnita, and M. S. Jailani, “Teknik Pemeriksaan Keabsahan Data dalam Penelitian Ilmiah,” J. QOSIM J. Pendidik. Sos. Hum., vol. 1, no. 1, pp. 53–61, Jul. 2023, doi: 10.61104/jq.v1i1.60.
B. Arianto, Triangulasi Metoda Penelitian Kualitatif. Balikpapan: Borneo Novelty Publishing, 2024.
National Institute of Standards and Technology (NIST), “SHA-3 Standard: Permutation-Based Hash and Extendable-Output Functions,” National Institute of Standards and Technology (U.S.), Washington, D.C., FIPS PUB 202, 2015. doi: 10.6028/NIST.FIPS.202.
E. Hayon and A. Darmianto, “Penerapan Algoritma Advanced Encryption Standard pada Aplikasi Pengamanan Data Teks Berbasis Web,” J. InTekSis, vol. 11, no. 2, pp. 46–56, 2024.
F. Bibiola, T. U. Kalsum, and H. Alamsyah, “Penerapan Algoritma Advance Encryption Standard (AES) untuk Pengamanan File pada Aplikasi Berbasis WEB,” J. SURYA ENERGY, vol. 8, no. 1, p. 35, Sep. 2023, doi: 10.32502/jse.v8i1.6461.
R. Khan, “Manish Adawadkar Kelley School of Business Indiana University, Bloomington, USA,” Int. J. Eng. Res., vol. 14, no. 08, 2025.
S. García-Ruiz et al., “AWS-S3-Integrity-Check: An Open-Source Bash Tool to Verify the Integrity of a Dataset Stored on Amazon S3,” Gigabyte, vol. 2023, pp. 1–15, Aug. 2023, doi: 10.46471/gigabyte.87.
M. Mahmud, Purnawansyah, and M. Hasnawi, “Implementasi Bot Telegram untuk Monitoring Jaringan dengan Pendekatan Security Policy Development Life Cycle Pada Kementerian Kelautan dan Perikanan Untia,” Bul. Sist. Inf. Dan Teknol. Islam, vol. 3, no. 2, pp. 127–133, 2022.
“What Is the Best Way to Protect My PHP Code?,” ionCube Blog. Accessed: Mar. 08, 2026. [Online]. Available: https://blog.ioncube.com/2020/12/07/best-php-code-protection/
“The Underbelly of PHP Security: How Obfuscation Makes Malicious Code Invisible,” Medium. Accessed: Mar. 08, 2026. [Online]. Available: https://medium.com/@keyboardsamurai007/the-underbelly-of-php-security-how-obfuscation-makes-malicious-code-invisible-d46f5da8e775
Md. S. Arman, S. A. Mamun, and N. Jannat, “A Modified AES Based Approach for Data Integrity and Data Origin Authentication,” in 2024 3rd International Conference on Advancement in Electrical and Electronic Engineering (ICAEEE), Gazipur, Bangladesh: IEEE, Apr. 2024, pp. 1–6. doi: 10.1109/ICAEEE62219.2024.10561750.
S. Dheyaa Mohammed, A. Monem S. Rahma, and T. Mohammed Hasan, “Maintaining the Integrity of Encrypted Data by Using the Improving Hash Function Based on GF 28,” TEM J., vol. 9, no. 3, pp. 1277–1284, Aug. 2020, doi: 10.18421/TEM93-57.
A. Z. Ifani, R. N. J. S.Intam, A. I. Syair, and H. Husnawati, “Application of Advanced Encryption Standard (AES) Algorithm in E-Commerce Login System for User Data Security,” J. Syst. Comput. Eng. JSCE, vol. 6, no. 1, pp. 1–9, Jan. 2025, doi: 10.61628/jsce.v6i1.1511.
G. Rubin, “How to Protect the Integrity of Your Encrypted Data by Using AWS Key Management Service and EncryptionContext,” AWS Security Blog. Accessed: Mar. 08, 2026. [Online]. Available: https://aws.amazon.com/blogs/security/how-to-protect-the-integrity-of-your-encrypted-data-by-using-aws-key-management-service-and-encryptioncontext/
Ajay Yadav, “Anti- Reverse Engineering (Assembly Obfuscation),” Application Security. Accessed: Mar. 08, 2026. [Online]. Available: https://www.infosecinstitute.com/resources/application-security/anti-reverse-engineering-assembly-obfuscation/
“Cryptographic PHP Functions,” functions-online. Accessed: Mar. 08, 2026. [Online]. Available: https://www.functions-online.com/cryptography.html
F. Febriyadi, F. Kurnia, N. S. Harahap, F. Yanto, and P. Pizaini, “Implementasi AES ECB dan Hashing MD5/SHA-256 Pada Aplikasi Penyuratan Android,” J. Comput. Syst. Inform. JoSYC, vol. 5, no. 1, pp. 113–126, Nov. 2023, doi: 10.47065/josyc.v5i1.4505.
A. R. Nurjaman and A. T. Turnip, “Kombinasi Algoritma Kriptografi AES-256 dan SHA3-512 untuk Meningkatkan Keamanan Dokumen PDF,” J. Ilm. Teknol. Infomasi Terap., vol. 11, no. 1, pp. 46–54, Dec. 2024, doi: 10.33197/jitter.vol11.iss1.2024.2346.
E. P. Nugroho, “Sistem Reporting Keamanan pada Jaringan Cloud Computing Melalui Bot Telegram dengan Menggunakan Teknik Intrussion Detection and Prevention System,” J. Teknol. Terpadu, vol. 5, no. 2, pp. 49–57, Dec. 2019, doi: 10.54914/jtt.v5i2.233.
J. T. Sirait and A. I. Santoso, “Perancangan Sistem Keamanan Rumah berbasis IoT dan Aplikasi Telegram,” J. Minfo Polgan, vol. 14, no. 1, pp. 676–681, May 2025, doi: 10.33395/jmp.v14i1.14834.
B. Schneier, Applied cryptography: protocols, algorithms, and source code in C, 2nd ed. New York: Wiley, 1996.
W. Stallings, Cryptography and Network Security: Principles and Practice, 5th ed. New York: Pearson Education, Inc, 2011.
G. G. Priatna, “Fungsi Enkripsi dan Dekripsi Menggunakan PHP: Panduan Lengkap untuk Pemula,” Fungsi Enkripsi dan Dekripsi Menggunakan PHP. Accessed: Mar. 09, 2026. [Online]. Available: https://qadrlabs.com/post/fungsi-enkripsi-dan-dekripsi-menggunakan-php
B. Esmaeili, “Advanced EXE Multi Protection Against Reverse Engineering with Free Tools,” Advanced EXE Multi Protection Against Reverse Engineering with Free Tools. Accessed: Mar. 09, 2026. [Online]. Available: https://www.cybrary.it/blog/advanced-exe-multi-protection-reverse-engineering-free-tools
D. Ariyus, Pengantar Ilmu Kriptografi: Teori Analisis dan Implementasi. Yogyakarta: CV Andi Offset.
Rizky Kurniawan, “Membuat Bot Telegram Sederhana Menggunakan PHP,” Ruang Developer. Accessed: Mar. 09, 2026. [Online]. Available: https://blog.ruangdeveloper.com/membuat-bot-telegram-sederhana-menggunakan-php/